Shared local administrator passwords are one of the most exploited weaknesses in Windows environments. Once an attacker has one, they can move laterally across your entire fleet, every device with the same password is instantly compromised. Windows LAPS fixes this by automatically generating a unique, rotating password for each device and backing it up securely to Entra ID.
This guide walks through every step: enabling LAPS in Entra, creating the Intune policy, verifying the deployment, and retrieving passwords when you need them.
What is Windows LAPS?
LAPS (Local Administrator Password Solution) is a Microsoft solution that programmatically generates a unique, complex password for the local administrator account on each managed Windows device. The password is stored as an encrypted attribute on the corresponding computer object in Entra ID (or on-premises Active Directory) and automatically rotated on a schedule you define.
The key security win: even if an attacker compromises one device's local admin account, that password is useless everywhere else. Lateral movement attacks that rely on credential reuse are stopped cold.
Step 1, Enable LAPS in Microsoft Entra
🔧 Entra Admin CentreBefore any Intune policy will work, you need to turn on LAPS at the tenant level in Entra ID. This is a single toggle that accesss the feature for all devices in your organisation.
- 1Sign into the Microsoft Entra admin centre as a Global Administrator or Cloud Device Administrator.
- 2Go to Entra ID → Devices → Device Settings.

- 3Scroll down to find Enable Microsoft Entra Local Administrator Password Solution (LAPS) and toggle it to Yes.
- 4Click Save.

Step 2, Enable the Local Administrator Account
🔧 Intune Admin CentreBy default, the built-in local administrator account is disabled on modern Windows installations. LAPS can't manage an account that doesn't exist in an active state, so this needs to be enabled first across your managed devices.
The most efficient way to do this across large fleets is with an Intune Account Protection policy. Sign into the Intune Admin Centre and go to Endpoint Security → Account Protection → Create Policy.

On the Create a profile screen, select:

On the Basics tab, name the policy clearly:

Step 3, Configure the LAPS Policy Settings
⚙️ Configuration SettingsThis is where you define the behaviour of LAPS, where to store passwords, how complex they should be, how often they rotate, and what happens after they're used. Work through each setting below.
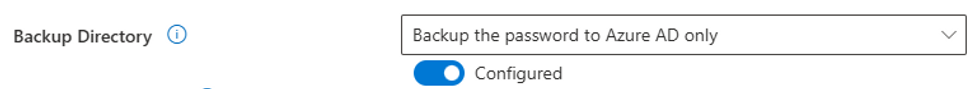
Backup Directory
Specifies where the generated password is stored. For cloud-only or Entra-joined devices, choose Azure AD only. For hybrid environments with on-prem AD, choose Active Directory only.
Password Age (Days)
How long before LAPS automatically generates a new password. The minimum for Entra backups is 7 days; for on-prem AD it's 1 day. The default of 30 days is a sensible starting point for most environments.

Administrator Account Name
Leave this blank to target the built-in administrator account, LAPS identifies it by its well-known SID, even if it's been renamed. Only enter a name here if you've created a specific custom local admin account you want LAPS to manage instead.

Password Complexity
Controls which character types LAPS uses when generating passwords. The improved readability option is the best choice for most organisations, it uses maximum complexity but excludes easily-confused characters (0/O, 1/l), making passwords easier to type manually when needed.

Password Length
Can be set between 8 and 64 characters. The default of 14 characters is the recommended starting point, long enough to resist modern brute-force attacks while remaining practical.

Post Authentication Actions
Defines what happens after an admin uses the LAPS password and the grace period expires. Options:
- Reset password, generates a new password silently, keeps the session active
- Reset password and log off, the most secure default; ends the session immediately
- Reset password and reboot, useful after maintenance tasks requiring a restart

Post Authentication Reset Delay (Hours)
The grace period, how long an admin has to work on the device before the post-auth action kicks in. Ranges from 0 (disabled) to 24 hours. The default of 24 hours gives admins ample time to complete tasks.

Settings Summary
Here's the full configuration at a glance, along with what the completed settings page looks like in Intune:

Step 4, Assign the Policy to Devices
👥 AssignmentsOn the Scope Tags tab, add any relevant tags if your organisation uses RBAC scoping, then click Next.

On the Assignments tab, click Add groups under Included groups. Start with a pilot security group to validate the policy before rolling out to your full device fleet.

On the final Review + Create tab, check all settings are correct and click Create to deploy the policy.

Step 5, Trigger an Intune Sync
🔄 Sync DeviceAfter creating the policy, devices will pick it up at their next scheduled Intune check-in. To force an immediate sync on a specific device, do it directly from the Admin Centre:
- 1Go to Devices → Windows in the Intune Admin Centre.
- 2Select the target device from the list.
- 3Click the Sync button in the top action bar, then confirm with Yes.

Step 6, Validate the Deployment
✅ VerificationDon't assume the policy applied, verify it from two places on the target device.
Event Viewer, LAPS Operational Log
LAPS has its own dedicated Event Viewer channel, separate from the standard Intune MDM logs. Open Event Viewer (run eventvwr.msc) and go to:
Applications and Services Logs → Microsoft → Windows → LAPS → OperationalFilter the log for Event ID 10022, this event provides a full summary of the LAPS policy settings applied by Intune, confirming the configuration arrived correctly.

Registry, LAPS Policy Key
You can also confirm the settings directly in the Windows Registry. Open Registry Editor (regedit.exe) and go to:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Policies\LAPSThe values here should match your policy configuration:
- PasswordAgeDays = 30
- PasswordLength = 14
- BackupDirectory = 1 (1 = Entra ID, 2 = Active Directory)
- PasswordComplexity = 5 (5 = max complexity with improved readability)

Retrieving the LAPS Password
🔑 Password RetrievalThere are three ways to retrieve a LAPS-managed password depending on your preference and workflow.
Method 1, Microsoft Intune Admin Centre
- 1Go to Devices → Windows and select the target device.
- 2On the device overview page, click Local admin password in the left panel.
- 3Click Show local administrator password to reveal the current password.

Method 2, Microsoft Entra Admin Centre
- 1Go to Identity → Devices → All devices.
- 2Under Help and support in the left nav, select Local administrator password recovery.
- 3Search for the device name, then click Show local administrator password.
- 4Click Show to reveal in plain text, or Copy to grab it without displaying it on screen.

Method 3, PowerShell (Microsoft Graph)
For scripted or automated retrieval, use the Get-LapsAADPassword cmdlet from the Microsoft Graph PowerShell module.
First, install the required module and connect to Microsoft Graph:
# Install the Microsoft Graph module if not already present
Install-Module -Name Microsoft.Graph -Force -AllowClobber
# Connect with the required permission scope
Connect-MgGraph -Scopes "DeviceLocalCredential.Read.All"A Microsoft sign-in window will appear, log in with your admin account and consent to the required permissions on first use.
Then retrieve the LAPS password for a specific device:
# Retrieve LAPS password for a specific device
# Replace YOUR-DEVICE-NAME with the actual computer name
$DeviceName = "YOUR-DEVICE-NAME"
$LapsResult = Get-LapsAADPassword -DeviceNameOrId $DeviceName -IncludePasswords -AsPlainText
if ($LapsResult) {
Write-Host "Device : $($LapsResult.DeviceName)" -ForegroundColor Cyan
Write-Host "Account : $($LapsResult.Account)" -ForegroundColor Cyan
Write-Host "Password : $($LapsResult.Password)" -ForegroundColor Yellow
Write-Host "Expires : $($LapsResult.PasswordExpirationTime)"
} else {
Write-Warning "No LAPS password found for '$DeviceName'. Has the policy synced yet?"
}